Neural-biometrics access management system: the new age of one notable technology
If you have ever thought about using biometrics as an additional security factor, you have probably heard skeptics’ opinions. Actually, they are not that untruthful.
Traditional biometrics access management systems have several vulnerabilities like imperfect liveness detection or the necessity to store sensitive data.
But there is SVORT which is a big difference from what we mean by biometrics.
Its feature is a particular neural network algorithm combined with biometrics and infallible liveness detection.
This great combo enabled the establishment of a perfect neural-biometrics access management system which is entirely invulnerable to spoofing attacks and data breaches. The following explains how SVORT works and what the key features make it outstanding.

How does neural-biometrics work?
The process of neural-biometrics authentication operates as follows. The particular neural network algorithm learns to detect users by their faces. A camera scan a person’s appearance at different angles. Then the system transforms the user’s face into code which itself is the private and depersonalized key.
Such a key is depersonalized because it does not contain any sensitive data. That is, even it is stolen it won’t enable attackers to get access to your data because the transformation of biometrics data into code is irreversible.
That is what makes SVORT invulnerable to data breaches.
Liveness detection as the main anti-spoofing tool
Photo, video, and mask spoofing are presented as the fundamental argument against biometrics access management systems. But a strong anti-spoofing tool already exists. It is liveness detection.
In terms of biometrics, liveness detection is the computer’s ability to determine whether it interacts with a human being. Camera understands whether it is a live person which physically present in front of it. Neither photo nor video and mask can override the system:
- The depth tracking sensor determines the volume making photo and video spoofing impossible.
- The infrared sensor prevents mask spoofing as it tracks the face heat map.
- Ordinary web cameras can also be used for liveness detection, 3D-face map building, and emotional challenges, i.e. there is no need to buy special equipment.

Combining neural networks, liveness detection and biometrics we get troublefree access management mean that prevents all kinds of spoofing and protects data reliably.
Where biometrics access management system with liveness detection can be used?
The biometrics technology has been gaining around the recent few years due to its convenience along with the high-security level. Using neural networks brings it to security perfection so it can be successfully applied to improve both personal and enterprise security.
Improving private security
Internet users can apply the SVORT authenticator as one of the security factors within multifactor authentication. Use such a system along with a strong password created by a password manager. You can be sure your data is reliably protected. The risk of a sensitive data breach is almost non-existent.
It is possible due to using your face as a key. Neither beard nor makeup, scars, or new hair dress impacts the users’ recognition process as the network algorithm memorizes not a face but its 3D models.
Raising enterprise security
Neural-biometrics access management systems can also be applied in businesses and government structures. It can protect sensitive business data if integrated into the company’s hardware environment. Such systems can also provide enterprises with safe access to offices, industrial buildings, and separate premises.
Keeping corporate data safe
Employees can use neural-biometrics access management systems within multifactor authentication to get access to a certain program, service, resource or computer itself.

Webcam scans an employee’s face to provide him with access. Then it maintains periodic inspections to authenticate the user. For this purpose, the system can use:
- rotational challenges (turn your head to the left, etc.);
- emotional challenges (raise your eyebrows, smile, etc.);
- hidden background inspections.
If an employee leaves workstation SVORT will automatically block his computer and it will be obligatory to pass authentication to unlock it.
SVORT can also replace existing authentication systems in offices providing employees with passwordless access. It will ease the overburdened technical support departments and save lots of time for employees as they will not have to use passwords and restore lost ones.
Industrial buildings security
Neural-biometrics access management systems can be integrated into existing security systems to provide employees and clients with keyless access to buildings. Right after the integration, the system starts memorizing people who continue using keys or personal cards for passing in.
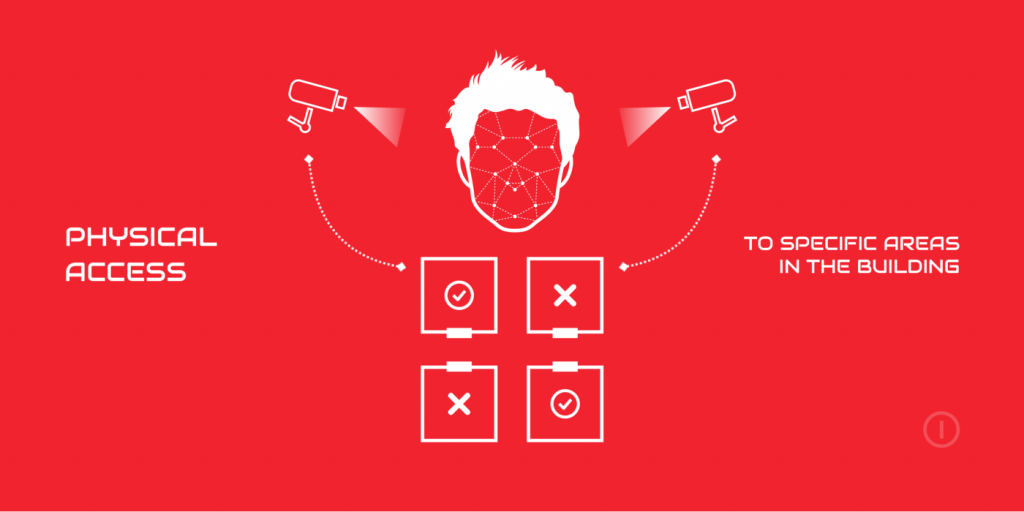
In a few days biometrics keys are created and the next time the system will unlock the door even before the person reach the physical key. The same principle is also available for use in separate premises. It is also possible to restrict entering a premise or allow it to certain people.
Actually, neural-biometrics combined with liveness detection can be applied in a variety of ways. Apart from the primary fields of application, it can also be used as follows:
- instead of personal loyalty cards;
- access to entrance halls for residents of an apartment complex;
- security in schools and kindergartens;
- clients detection;
- anonymous and safe access to online services and resources that support MFA;
- remote identification and verification;
- check a driver’s condition within the freight, public transport or carsharing services;
- identification and subsequent anonymization users for anonymous voting;
- etc.
It is the combination of neural-biometrics, liveness detection and industry expertise that can provide users and enterprises with the required security level not affecting users’ experience. And SVORT is that very new age of access management systems that will prevent tremendous damage from data breaches creating the ultimately secure digital environment.